Activated the openid in appsettings. When you click on openid button, i'm redirected to authority server, i can login and i'm redirected.
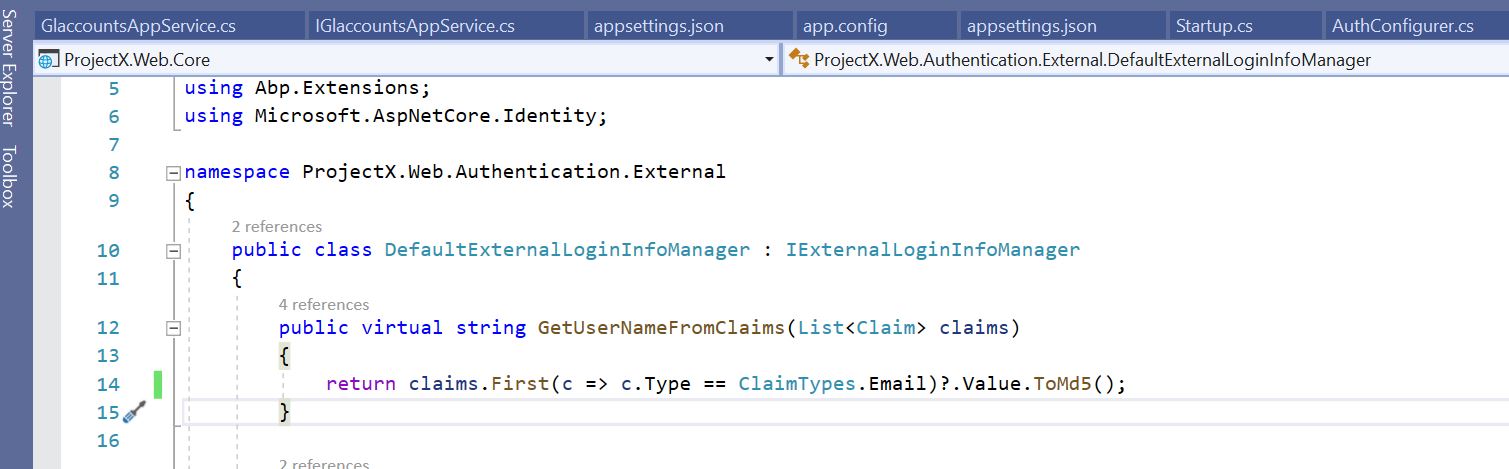
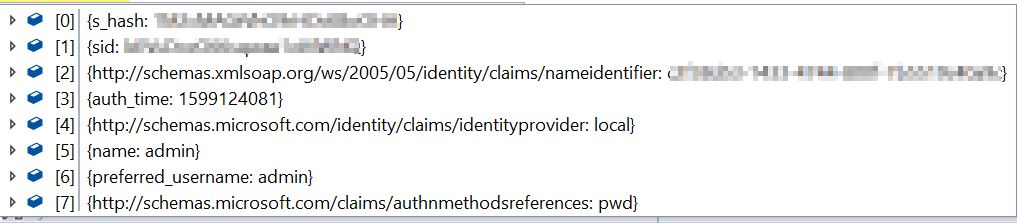
The principal has 8 claims, but not the email claim.
No code from the asp.net zero framework has been adjusted
What could be the reason ?
Thx for the advice, Frederick
8 Answer(s)
-
0
Hi @devloo
Could you share the name of claims returned from external provider ? You can use ClaimsMapping in the appsettins.json to map external claim to email claim. See https://github.com/aspnetzero/aspnet-zero-core/blob/dev/aspnet-core/src/MyCompanyName.AbpZeroTemplate.Web.Mvc/appsettings.json#L57
-
0
-
0
Hi,
If nameidentifier contains the email value, you can map it to internal email claim like below;
"ClaimsMapping": [ { "claim": "unique_name", "key": "http://schemas.xmlsoap.org/ws/2005/05/identity/claims/nameidentifier" } -
0
I added following claim, but the no extra claims with email info is added { "claim": "email", "key": "http://schemas.xmlsoap.org/ws/2005/05/identity/claims/emailaddress" }
Why is the openid integration not working out of the box ? That's one of the reasons we bought the asp.net zero licence. Is the setup of our Identity server correctly ?
Some other related questions
- If we enable the 'identity server' setting in the appsettings (for authentication of dynamic web api controllers), the openid login is not working at all
- how can we import/activate the existing identity server users in asp.net zero MVC application (without that users need to be activated and fill in the firstname/lastname/email when first time logged in the mvc web application)
-
0
Hello @devloo At first glance, there may be two reasons why you might not be getting email claim;
- You're not requesting email scope as a client
- You're requesting email scope but identity provider doesn't handle what to return when email scope is requested.
Try navigating to https://YOUR_DOMAIN/.well-known/openid-configuration and check if email scope is supported. Also, what is your authorization server? Is it an other AspnetZero application?
About connecting AspnetZero application to each other, answers at the post may be useful: https://support.aspnetzero.com/QA/Questions/9394/Delegate-another-project's-auth-to-zero-project
-
1
This is what I had to do to make OpenID work for google.
- Add "email" to request scope in authenticationBuilder.AddOpenIdConnect method. I passed it as an argument from the settings
options.Scope.Add("email");- Looking at the source code for SigninManager's GetExternalLoginInfoAsync method, I have identified that it is looking for a Claim by name "nameidentifier". This claim is being returned when using the Google Authentication directly. So added the below mapping. Not sure where the "unique_name" will be used *
{ "claim": "http://schemas.xmlsoap.org/ws/2005/05/identity/claims/nameidentifier", "key": "http://schemas.xmlsoap.org/ws/2005/05/identity/claims/emailaddress" }You just have to change the "RegisterForExternalLogin" method to add users automatically without the activation.
I hope we get the documention on this functionality soon.
Thanks, Raj.
-
0
Thanks @rajalla :)
-
0
Thanks @rajalla !! Your solution worked.