-
What is your product version?
v9.3.0 -
What is your product type (Angular or MVC)?
Angular -
What is product framework type (.net framework or .net core)?
.net core
We are trying to make external login with open id connect.
Our client uses PingFederate (PingIdentity) for the identity server.
We are using the open id login process with Auth Code Flow + PKCE.
The user is logged in from the authorization endpoint and successfully redirects to our application.
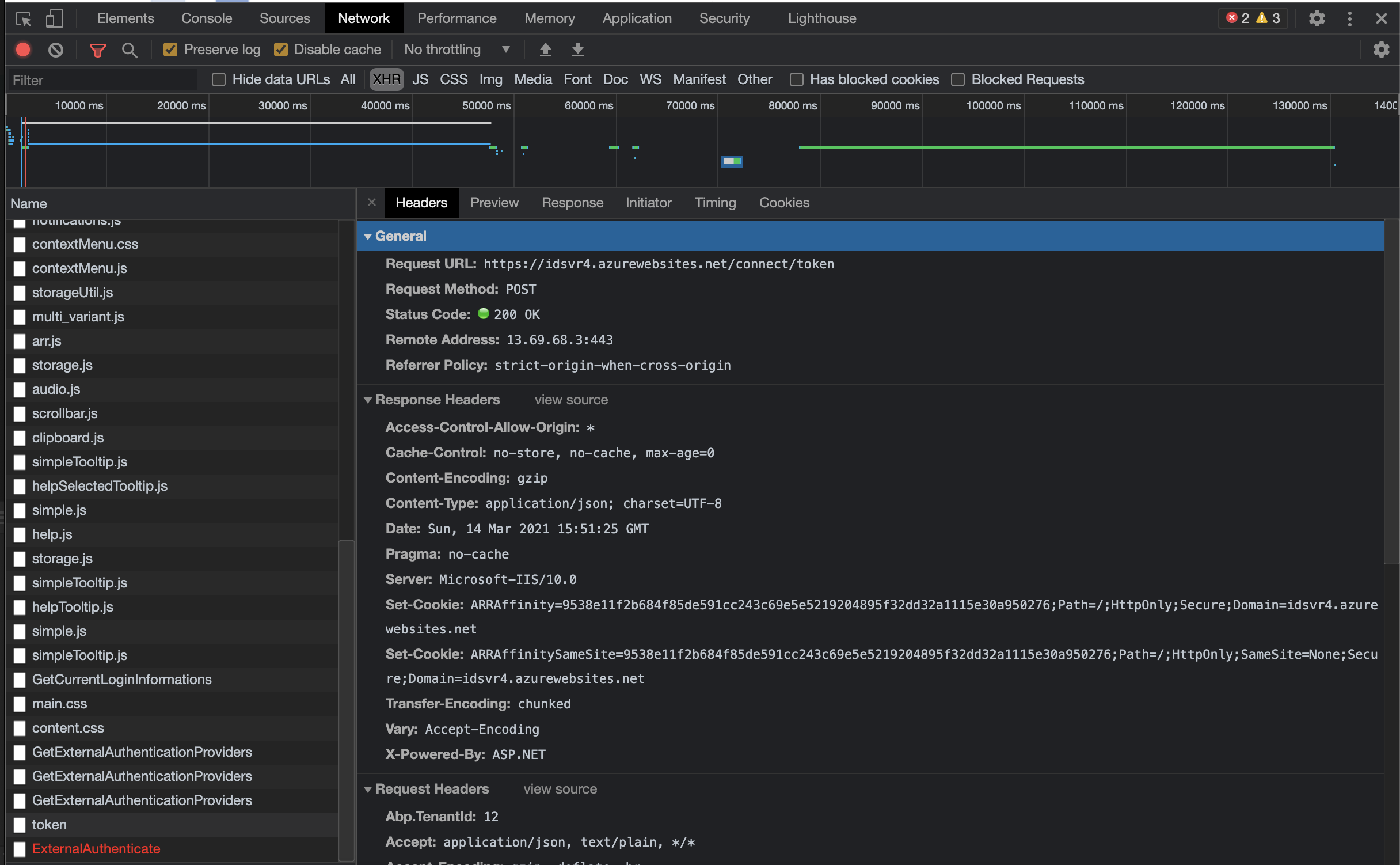
Then the request sent to the token endpoint gets stuck with a cors error.
Actually, by default, our client grants cors permissions for the token endpoint, but we get a cors error due to the extra headers such as "abp.tenantid" in the request sent.
How can I remove the "abp.tenantid" header from this request? what can you suggest to remove this header?
4 Answer(s)
-
0
Hi @echonos
abp.tenantid request header is required for tenant determination.
Is it possible for you to temporarily allow this header and see if it works ? -
0
Hi @ismcagdas
We do not need the "abp.tenantid" header for the request made to the OpenId provider. This request is not made to abp.zero backend Api, it's made to OpenId provider token endpoint by angular-oauth2-oidc library.
Yes, after a troubleshooting session, our customer says the request is work correctly if removing this header
-
0
Hi @echonos
Then the request sent to the token endpoint gets stuck with a cors error.
Could you share how do you make this request ?
Probably AspNet Zero's HttpInterceptor adds the
abp.tenantidrequest header. If so, you need to extend https://github.com/aspnetboilerplate/abp-ng2-module/blob/master/projects/abp-ng2-module/src/lib/interceptors/abpHttpInterceptor.ts and create your own HttpInterceptor.Then, you can just override
normalizeRequestHeadersand conditioanly send this header. -
0
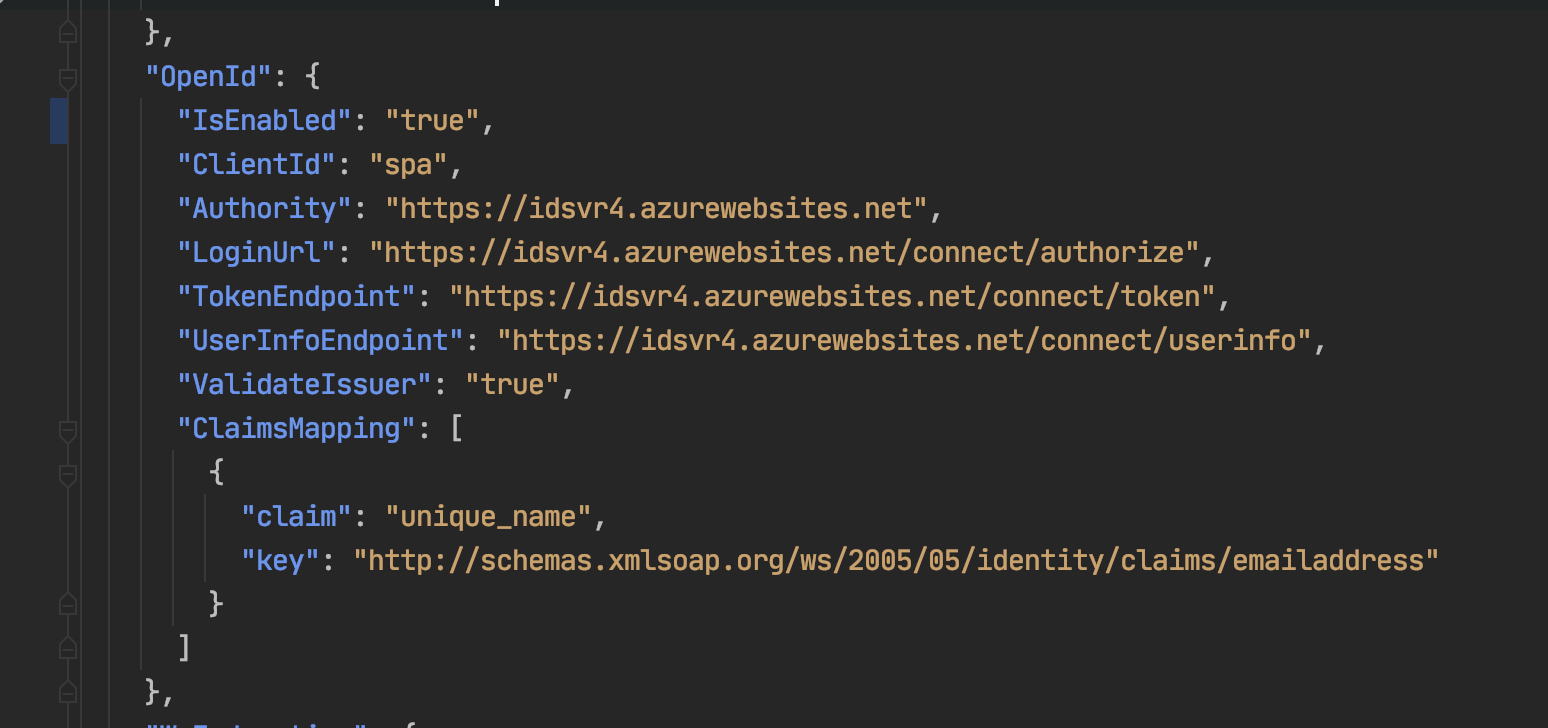
That is the openId configuration and token endpoint request for IdentityServer4 demo site ( https://idsvr4.azurewebsites.net )
Thank you, Ismail,
With your suggestion I extended the AbpHttpInterceptor and removed the headers from the request, this solved my problem